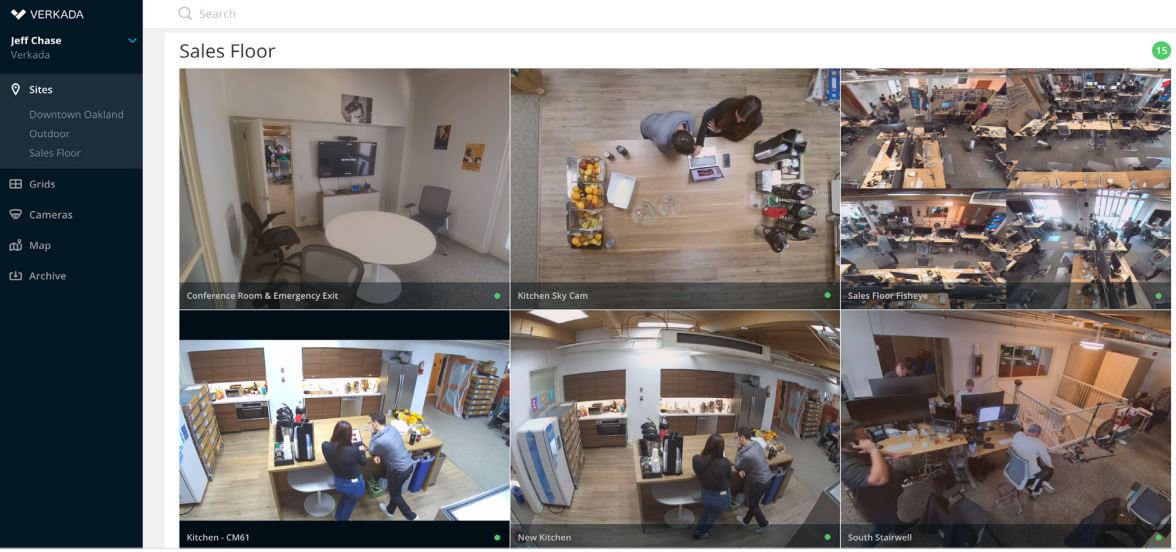
A group of hackers are reported to have breached a massive trove of security-camera data collected by Silicon Valley startup Verkada Inc., gaining access to live feeds of 150,000 surveillance cameras inside hospitals, companies, police departments, prisons and schools.
The report by Bloomberg has established companies whose footage was exposed include carmaker Tesla Inc. and software provider Cloudflare Inc. In addition, hackers were able to view video from inside women’s health clinics, psychiatric hospitals and the offices of Verkada itself. Some of the cameras, including in hospitals, use facial-recognition technology to identify and categorize people captured on the footage. The hackers say they also have access to the full video archive of all Verkada customers.
“We have disabled all internal administrator accounts to prevent any unauthorized access,” a Verkada spokesperson said in a statement. “Our internal security team and external security firm are investigating the scale and scope of this issue, and we have notified law enforcement.”
Asaf Hecht, Cyber Research Team Leader from CyberArk commented to CCTVBuyersGuide, “The potential for breaching common IoT devices, like security cameras, is something we’ve been talking about for years. Cameras, much like other hardware devices, are often manufactured with built-in or hard coded passwords that are rarely, if ever, changed by the customer.”
“While we can’t be sure that’s what happened in this case, recent breaches certainly have ‘scale’ in common, demonstrating attackers’ growing confidence and precision – and ability to efficiently extrapolate weaknesses for impact. And while Verkada reportedly took the right steps to disable all internal administrator accounts to prevent any unauthorized access, it was likely too late. The attackers had already landed.
“Based on what’s been reported, this attack follows a well-worn attack path – target privileged accounts with administrative access, escalate privileges to enable lateral movement and obtain access to highly sensitive data and information – effectively completing the intended goal. What we’ll need to especially watch in this case is the potential for far-reaching implications for privacy regulations including HIPAA.”